Security That Works In the Real World
Offensive security services and talent programs delivered by practitioners — not slide-deck consultants. Every engagement is adversary-driven, outcome-focused, and built for your actual risk profile.
Everything We Offer
From penetration testing to structured mentorship — each service is built around real outcomes, not deliverable counts.
VAPT
Comprehensive vulnerability assessment and penetration testing across web, network, and infrastructure.
- Security posture and attack surface assessment
- Adversary-driven threat modeling
- Web, network, and infrastructure testing
Red Team Simulation
Adversary simulation engagements that test your detection and response capabilities end-to-end.
- Initial access simulation (phishing, external exposure)
- Lateral movement and privilege escalation
- Active Directory compromise scenarios
Mentorship
1-on-1 mentorship from practitioners. Built for students who want to accelerate their careers fast.
- Personalized learning and career roadmap
- Skill-gap analysis based on your current level
- Resume and profile reviews from a hiring perspective
Internship Program
6-week intensive internship with real projects, real clients, and a certificate that actually means something.
- Exposure to real-world security tasks
- Guided execution instead of hand-holding
- Feedback on how you approach problems
Webinars & Workshops
Monthly live sessions on current techniques, tools, and attack research. Open to the community.
- Monthly live webinars
- Tool deep-dives and demos
- Q&A with practitioners
Security Consulting
Strategic security consulting for startups and SMEs building their security posture from scratch.
- Security program design
- Policy and process development
- Security tool stack recommendations
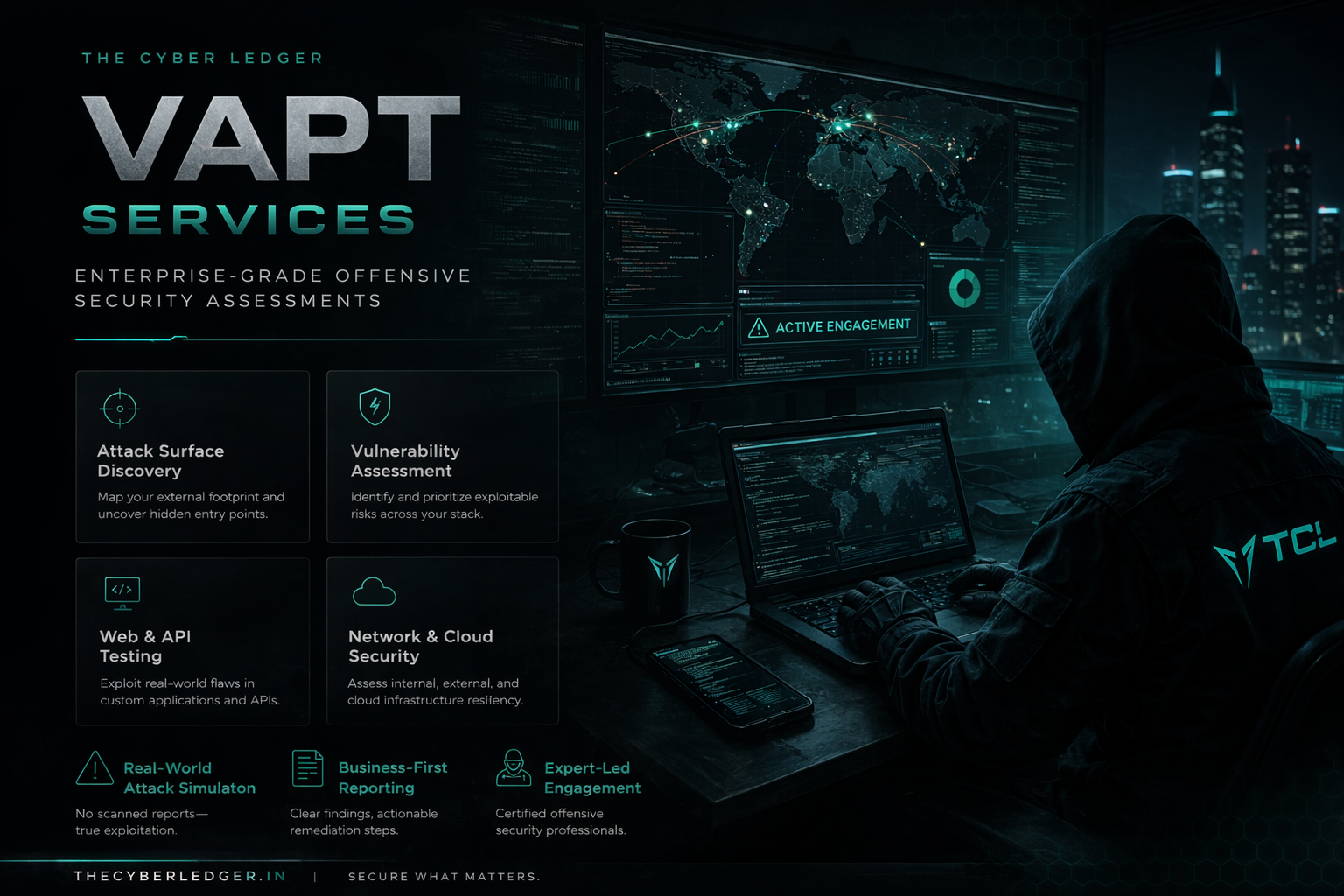
VAPT
Our VAPT engagements go beyond automated scans. We analyze how your systems could actually be abused — identifying exploitable paths, chaining vulnerabilities, and delivering actionable remediation guidance your team can implement immediately.
- Security posture and attack surface assessment
- Adversary-driven threat modeling
- Web, network, and infrastructure testing
- Risk prioritization based on real impact
- Actionable remediation guidance
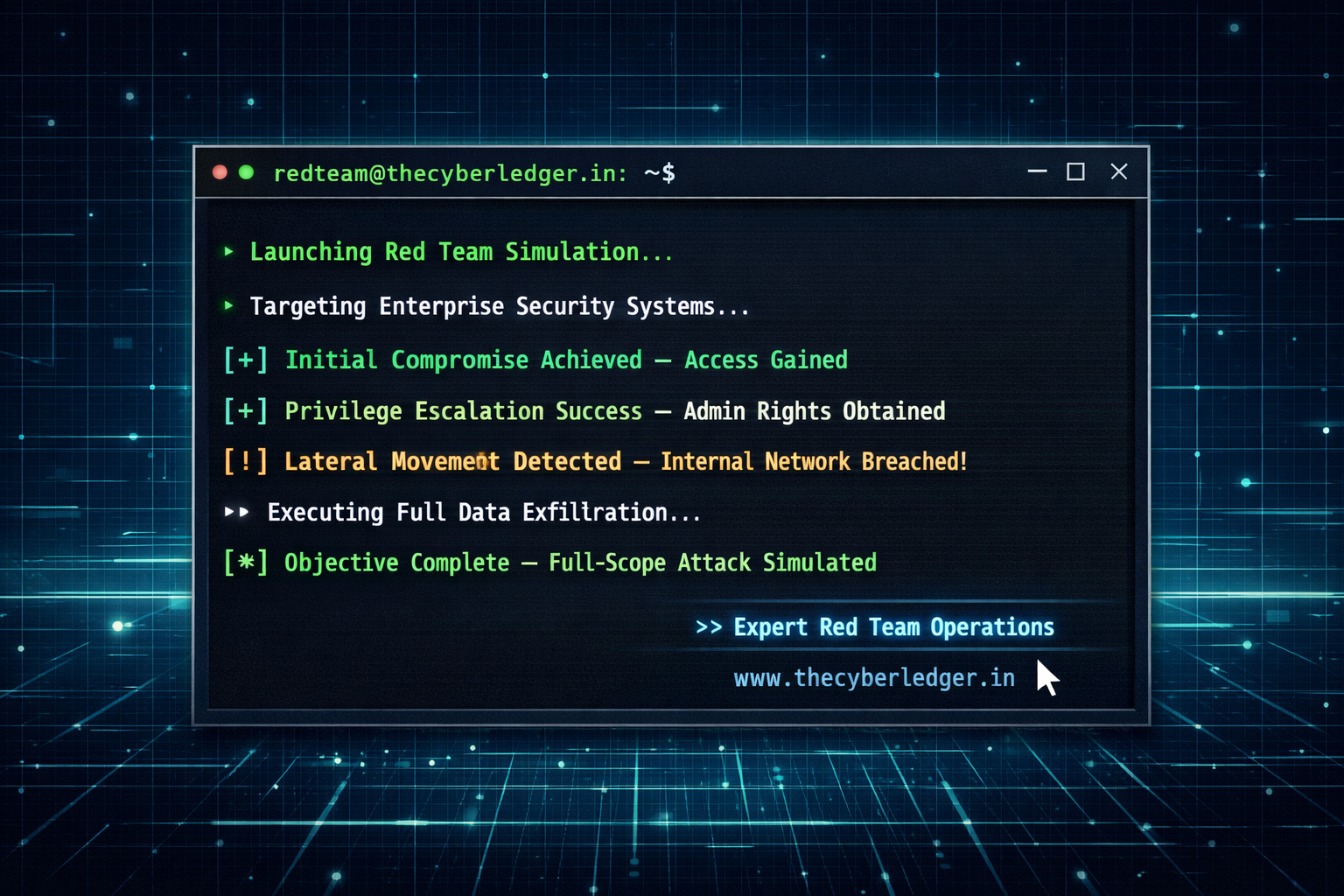
Red Team Simulation
Full kill-chain adversary simulations from initial access to domain compromise. We test not just your defenses but your team's ability to detect, respond, and contain a real threat actor.
- Initial access simulation (phishing, external exposure)
- Lateral movement and privilege escalation
- Active Directory compromise scenarios
- Detection and response gap analysis
- Full kill-chain reporting

Mentorship
This is not motivational coaching or generic career advice. Mentorship at TCL is hands-on, honest, and tailored to where you are right now — technically and professionally.
- Personalized learning and career roadmap
- Skill-gap analysis based on your current level
- Resume and profile reviews from a hiring perspective
- Guidance for red team, blue team, SOC, or general security roles
- Interview preparation and real-world expectations

Internship Program
Our internships are designed to simulate real security work as closely as possible. This is not a watch-and-learn program — you do the work, with guidance.
- Exposure to real-world security tasks
- Guided execution instead of hand-holding
- Feedback on how you approach problems
- Understanding of how security work flows in practice

Webinars & Workshops
Every month, our practitioners go live with deep dives on attack techniques, tool releases, and industry trends. No slides. All terminal. All practical.
- Monthly live webinars
- Tool deep-dives and demos
- Q&A with practitioners
- Community recordings archive

Security Consulting
We help organizations build security programs that actually work — starting from their real risk profile, not a generic compliance checklist.
- Security program design
- Policy and process development
- Security tool stack recommendations
- Team training and enablement
- Ongoing advisory support
Our Engagement Process
Every security engagement follows the same disciplined methodology — starting with understanding your environment, not scanning it blind.
Assessment
We understand your environment, assets, and risk profile before touching anything.
Testing
Adversary-driven testing that mirrors how real attackers operate — not checkbox scanning.
Reporting
Clear, actionable reports with real impact context — not severity scores with no guidance.
Remediation
We walk your team through fixes, validate patches, and confirm the attack path is closed.